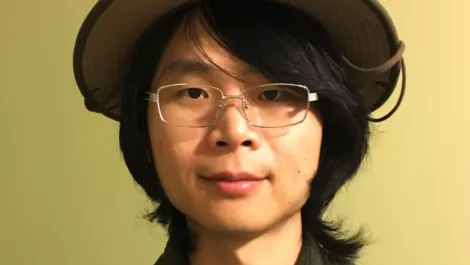
About Kai Ping

Kai Ping Lew
Editor-in-Chief & News Editor - Security
KP was raised in Malaysia and graduated with a degree in Journalism and International Business at AUT. After graduating, she did a stint in broadcast media at TVNZ before deciding to return to her true love, the written word. In her spare time, KP enjoys exploring fictional universes through books, spending time in the sun, playing volleyball, and dancing.
Former TechDay team member.
Stories by Kai Ping - Page 5

Exabeam and Okta partner to add context to identity management
Thu, 23rd Aug 2018
#
partner programmes
#
iam
#
cybersecurity
The joint Exabeam and Okta solution will help security teams to monitor and protect enterprises against credential-based threats.

Is BYOD an expensive mistake for your business?
Wed, 22nd Aug 2018
#
byod
#
mobility
#
wavelink
Although BYOD can seem like a cost-effective mobility solution, experts warn it might backfire due to security, productivity, and cost concerns.

Exclusive: How AI and quantum computing are changing cybersecurity
Tue, 21st Aug 2018
#
siem
#
iaas
#
quantum computing
AI and quantum computing are transforming cybersecurity, promising enhanced threat detection and faster responses, but also presenting new challenges.

Hackers using spearphishing to target banks –Bitdefender
Tue, 21st Aug 2018
#
malware
#
cybersecurity
#
bitdefender
To limit the risk of being discovered, attackers operated outside of normal business hours and cashout operations were planned for weekends.

Vehicle security startup Trillium recognised by innovation platform
Mon, 20th Aug 2018
#
cartech
#
trillium
#
plug and play
Trillium, a cybersecurity leader in vehicle data protection, has been named Plug and Play's Hottest Company for August, standing out among hundreds of startups.

Over 2,300 data breaches disclosed so far in 2018 - report
Mon, 20th Aug 2018
#
phishing
#
email security
#
breach prevention
Phishing for and using the stolen credentials to access systems or services stands out as a particularly popular attack method.

Gigamon partners with Endace for improved network visibility
Mon, 20th Aug 2018
#
firewalls
#
network infrastructure
#
devops
Analysts often struggle to uncover the evidence they need to quickly determine the root cause of cyber threats.
Exclusive: What will it take for blockchain to achieve mass adoption?
Fri, 17th Aug 2018
#
blockchain
#
supply chain
#
opinion
With the technology and its applications still an enigma to most, blockchain has a long way to go before it's mature enough for many use cases.

FireEye brings machine learning to endpoint security solution
Thu, 16th Aug 2018
#
endpoint protection
#
breach prevention
#
edr
The machine learning model is trained with both public and private data sources, including data gathered from over 15 million endpoint agents.

Flaw discovered in Intel chips, allows attackers to steal cloud data
Thu, 16th Aug 2018
#
semiconductors
#
intel
#
cpu
A newly discovered flaw in Intel chips, dubbed Foreshadow, can lead attackers to access sensitive data from personal computers and cloud services.
Exclusive interview: Major MFA vulnerability discovered in Microsoft's ADFS
Wed, 15th Aug 2018
#
mfa
#
iam
#
cybersecurity
A critical flaw in Microsoft's ADFS allows bypassing MFA, posing a severe risk, warns Okta's REX team. Urgent patching is recommended for users.
Security professionals are considering black hat activity - report
Mon, 13th Aug 2018
#
edr
#
malwarebytes
#
report
49% of global mid-market professionals were most likely to suggest that it's easy to get into cybercrime without getting caught.
Exclusive: How nation-state attacks impact businesses
Mon, 13th Aug 2018
#
cyber attacks
#
cybersecurity strategy
#
nation state attacks
With tensions between global superpowers rising, cyber attacks have become a new frontier for governments to gain an advantage over one another.

Trustwave releases facial recognition tool for pentesters
Thu, 9th Aug 2018
#
devops
#
surveillance
#
biometrics
Social Mapper takes an automated approach to searching popular social media sites for names and pictures of individuals.

CrowdStrike expands global partner footprint
Wed, 8th Aug 2018
#
endpoint protection
#
partner programmes
#
ai security
CrowdStrike also announced an expansion of its relationship with Dragos, launching a joint Incident Response (IR) retainer offering.

BlackBerry integrates ransomware recovery into collaboration platform
Tue, 7th Aug 2018
#
malware
#
uc
#
ransomware
Most ransomware recovery solutions enforce a companywide rollback, meaning even users whose systems were not impacted may lose data.

Exclusive: Tackling the challenges faced by women in cybersecurity
Fri, 3rd Aug 2018
#
dei
#
stem
#
gender diversity
Some companies though do an incredible job of recruiting women into their workforces, but they have problems retaining them.

CyberArk launches SAP-certified privileged access security solution
Fri, 3rd Aug 2018
#
pam
#
partner programmes
#
risk & compliance
Credentials for SAP applications and systems are sought out by attackers to gain access to business-critical information and assets.

User passwords and email addresses compromised in Reddit breach
Thu, 2nd Aug 2018
#
mfa
#
iam
#
breach prevention
Its primary access points for code and infrastructure had required two-factor authentication via SMS, and the main attack intercepted the text.
DDoS attacks combining new and tried-and-true techniques
Thu, 2nd Aug 2018
#
gaming
#
ddos
#
digital entertainment
DDoS botnets attacked online resources in 74 countries in Q2 2018, reveals Kaspersky Lab report. Hong Kong now ranks second among the most attacked countries.