Zscaler flags Xloader malware's tougher obfuscation
Zscaler's ThreatLabz research team has published new analysis of the Xloader malware family, which has added new obfuscation and network communication methods.
Xloader is an information-stealing malware strain that evolved from Formbook, first seen in 2016 and rebranded in early 2020. ThreatLabz said the most recent version it observed was 8.7, and that changes introduced from version 8.1 onward have made automated analysis more difficult.
The malware targets data stored in web browsers, email clients, and FTP applications. It can also execute arbitrary commands on infected machines and download additional payloads, extending its role beyond credential theft.
Obfuscation changes

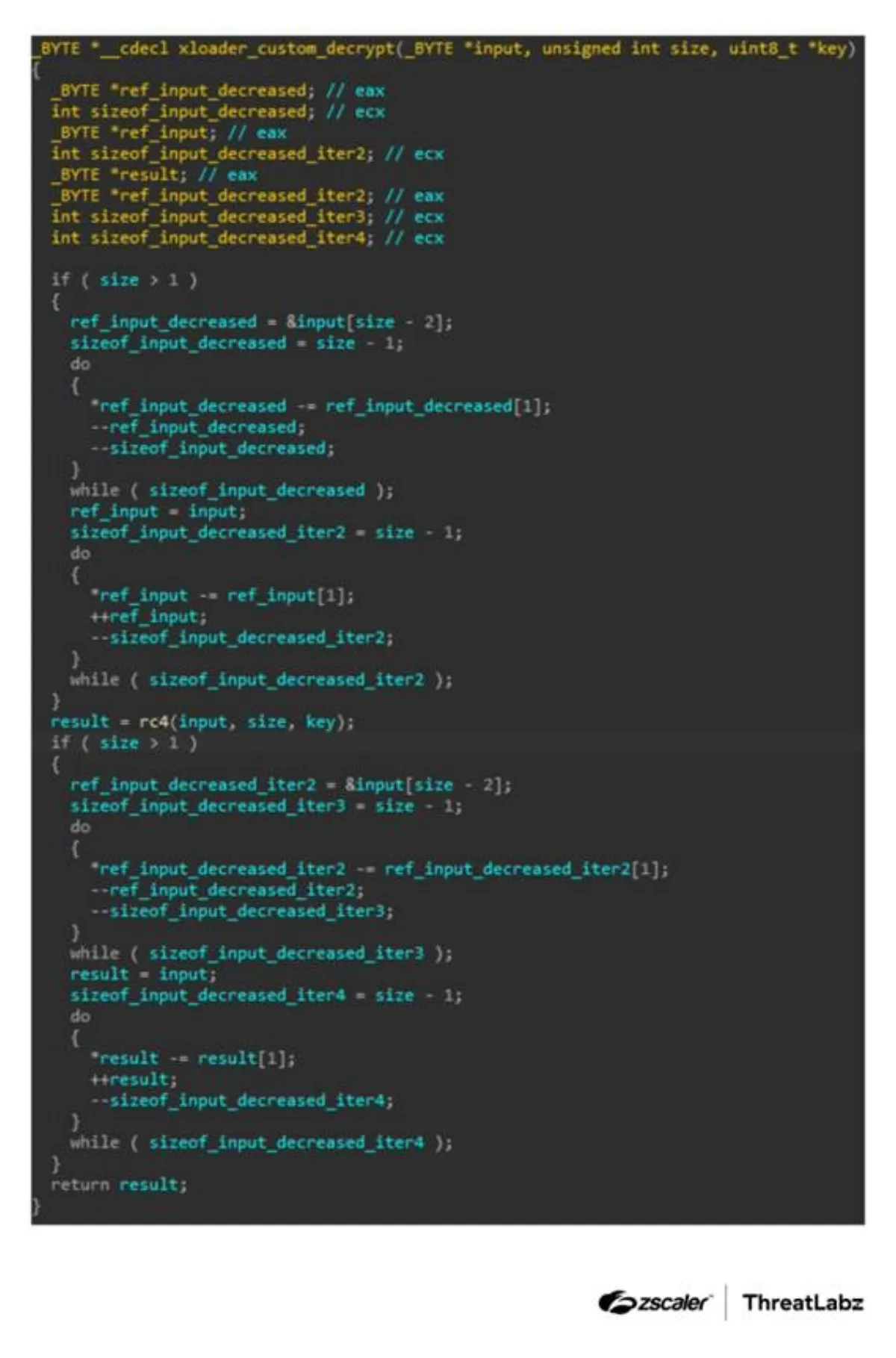
Xloader continues to rely on runtime decryption of strings and code blocks, while adding more complex methods to conceal how key functions operate. One change affects how the malware constructs the parameters needed to decrypt functions in memory.
Earlier versions built these parameters in a more consistent order. Since version 8.1, Xloader has created them out of sequence and, in some cases, byte by byte, forcing analysts to reconstruct memory layouts before they can extract values.
These changes complicate pattern matching and other routine reverse-engineering techniques. The report also described broader use of opaque predicates and XOR-based logic to hide hardcoded values and parts of the malware's decryption routines.
Another change appears in the malware's custom decryption function. The latest versions pass a structure containing hardcoded values, then decrypt each required member during execution rather than exposing the values more directly in code.
Network tactics
Xloader uses two main methods to communicate with command-and-control servers. Depending on a preconfigured flag, it can use raw TCP sockets or Windows WinINet API functions. Each method produces similar traffic but different User-Agent headers.
When using raw sockets, the malware checks whether the Windows API function gethostbyname has been inline-hooked. If it detects signs of a hook, it does not send the HTTP request, a step designed to avoid some defensive monitoring techniques.
Xloader also applies several layers of encryption to outgoing traffic even though the underlying web requests use plaintext HTTP. ThreatLabz said it combines RC4 encryption with keys derived from the command-and-control URL and adds Base64 encoding at different stages.
The research identified separate handling for GET and POST requests. GET requests retrieve command packets known internally as PKT2 messages, while POST requests send stolen credentials and cookies from compromised systems.
To make detection harder, Xloader uses a list of 65 command-and-control IP addresses and decrypts them only when needed. It then randomly selects 16 addresses at a time and sends traffic until all listed servers have been contacted.
This approach makes it difficult for sandboxes to distinguish decoy infrastructure from genuine command-and-control servers. Analysts may need to emulate network connections to each address and inspect responses to identify the real servers.
Broad command set
Once it receives a response from a command server, the malware supports a range of remote commands. The analysis listed instructions to execute PowerShell scripts, Windows executables, and DLL files; update the malware; remove itself; delete browser cookies; steal credentials; reboot a compromised host; and shut it down.
One command path allows the malware to download and run a remote PowerShell script or executable from a specified location. Another enables execution of a file already present on the infected machine.
The report also noted signs of legacy code within Xloader, reflecting its origins in Formbook. Some request identifiers and command elements appear to be unused across observed samples.
Xloader's continued development points to a malware family that remains active and adaptable. ThreatLabz wrote that the combination of layered encryption, decoy servers, and heavier obfuscation has helped keep it difficult to analyse, while the latest observed version remains 8.7.