Latest news - Page 764

Cybercrims bypassing two-factor authentication with simple txt
Thu, 18th Jun 2015
#
mfa
#
iam
#
cybersecurity
Strong passwords and two-factor authentication are no match for simple social engineering, with Symantec warning of a new password recovery scam.

Landesk looks at employee satisfaction and BYOD
Wed, 17th Jun 2015
#
byod
#
productivity
#
landesk
The majority of employees are satisfied with their IT departments, and BYOD is aiding productivity but is still a security gap, says Landesk.

Blue Coat named a Magic Quadrant Leader yet again
Tue, 16th Jun 2015
#
gartner magic quadrant
#
analyst report
#
ss&c blue prism
In order to select 'leaders', Gartner evaluates vendors on their ability to execute as well as the completeness of vision of their products in the SWG.

Are drones the new weapon of choice for Kiwi burglars?
Mon, 15th Jun 2015
#
drones
#
surveillance
#
vivint
Kiwi burglars could start using drones to target homes due to lack of regulations, warns home security expert.

Wynyard Group and Motorola Solutions, using data to fight crime
Fri, 12th Jun 2015
#
data analytics
#
martech
#
planning
Motorola Solutions' Smart Public Safety Solutions and Wynyard Group's analytics software will help public safety quickly gain actionable intelligence.

Cisco embeds 'security everywhere' to protect IoT world
Wed, 10th Jun 2015
#
iot
#
edge security
#
cisco
Cisco is taking 'security everywhere' with a slew of new offerings to embed security across the network, turning it into a sensor and enforcer.

Are Kiwi SMBs dismissing BYOD threats?
Mon, 8th Jun 2015
#
cybersecurity
#
byod
#
kaspersky
Small business owners are not concerned about the security risks of BYOD, leaving their company vulnerable, according to a study by Kaspersky Lab.

Lifting the lid on major enterprise security threats
Thu, 4th Jun 2015
#
malware
#
firewalls
#
network security
Today's cybercriminals are sophisticated and ruthless: they prey on the weaknesses in a network, approaching any security layer as an open invitation.

Cisco: Securing the Internet of Everything
Wed, 3rd Jun 2015
#
iot
#
cybersecurity
#
dubai
The Internet of Everything (IoE) is increasing the need for intelligent security and privacy solutions, according to Cisco.

Check Point: Protecting ICS from cyber threats
Tue, 2nd Jun 2015
#
advanced persistent threat protection
#
operating systems
#
security vulnerabilities
Check Point Software introduces new security gateway for Industrial Control Systems; aims to prevent cyber attacks on critical infrastructure.

ESET uncovers another porn clicker on Google Play
Mon, 1st Jun 2015
#
google
#
eset
#
retail
ESET has uncovered multiple variants of a Trojan porn clicker on Google Play, masquerading as Dubsmash 2, rapidly exploited by cybercriminals.

Intelligence-led testing imperative for security
Fri, 29th May 2015
#
cybersecurity
#
bae systems
#
bank of england
The evolving cyber threat landscape is leading to a real need of more robust defences, as well as realistic, or 'real-life' testing of those defences.

Fortinet snaps up Meru; launches BYOD service
Thu, 28th May 2015
#
firewalls
#
network infrastructure
#
network security
Fortinet is the latest company in acquisition mode, announcing it will acquire Wi-Fi networking company Meru Networks, in a US$44 million deal.

Scammers using VoIP to target mobile phone users
Thu, 28th May 2015
#
uc
#
email security
#
cybersecurity
Scammers are using technology to do their dirty work, and new applications are making it easier to orchestrate scams to steal personal information.

Symantec still number one in changing security software market
Thu, 28th May 2015
#
dlp
#
cybersecurity
#
symantec
Gartner believes that 2014 is the last year that the market will exhibit such solid double-digit growth in its current form.

Commvault addresses file sharing security concerns
Wed, 27th May 2015
#
endpoint protection
#
edr
#
commvault
IT is losing its grip on corporate data through the combination of poor data governance and an increasing reliance on insecure file sharing solutions.

BYOD security policies vital
Wed, 27th May 2015
#
cybersecurity
#
byod
#
uxc connect
BYOD policies require commitment from all employees to follow security policies says Rick Bell, architect for UXC Connect.

Ransomware masquerades as FBI, Android users in the crossfire
Tue, 26th May 2015
#
malware
#
ransomware
#
cybersecurity
Thousands of Android users have been targeted by a ransomware that demands users to pay $500 to restore access to their smartphone, says Bitdefender.

Huawei unveils APT big data security solution
Tue, 26th May 2015
#
ddos
#
data analytics
#
martech
Huawei has released a new solution designed to protect against Advanced Persistent Threat (APT) and denial-of-service (DdoS) attacks.
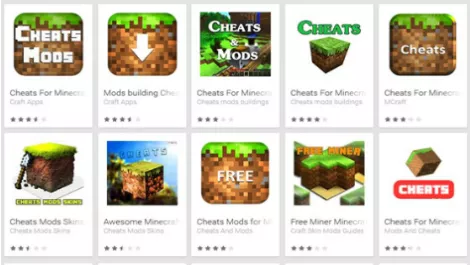
Mind those Minecraft cheats, malware may lurk inside
Mon, 25th May 2015
#
malware
#
cybersecurity
#
minecraft
Security vendor Eset is warning Minecraft fans to cheat with care after discovering 33 Android Minecraft cheat apps packing scareware.