AppOmni has warned that attackers compromised Aqua Security's Trivy GitHub repository and used it to distribute malicious code, creating risks for organisations that rely on Trivy in software build pipelines.
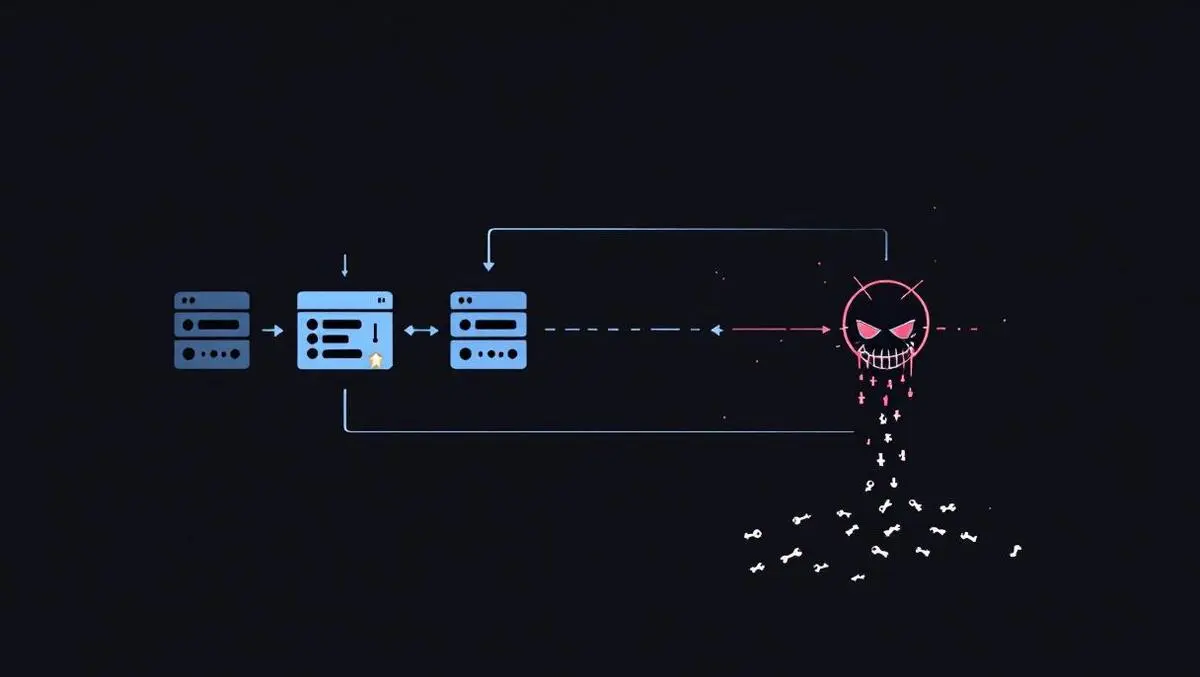
The attack centred on aquasecurity/trivy-action, a GitHub Action used in CI/CD workflows. Attackers altered version tags so automated workflows would pull poisoned code while appearing to run normally. That could expose credentials and API keys, opening access to SaaS applications, cloud environments and administrative systems.
Trivy is widely used as a security scanner in software development pipelines. AppOmni said the main Trivy project has roughly 32,000 GitHub stars, while the affected trivy-action repository has about 1,300.
Cory Michal, Chief Security Officer at AppOmni, said the incident is significant because attackers did not need to target organisations one by one.
"The GitHub repository for Trivy, a widely used security tool in software build pipelines, was compromised and turned into a delivery mechanism for malicious code. After gaining access to Aqua Security's GitHub repository, the attackers inserted infostealer code into aquasecurity/trivy-action and altered version tags so organisations' GitHub workflows would automatically download the poisoned code while still appearing to run normally. Since GitHub is a core SaaS platform in the software delivery chain, a compromise there can expose credentials and API keys that provide access to other SaaS applications, cloud environments and administrative systems."
"This poses a meaningful industry-wide risk because Trivy is a broadly trusted security scanner embedded in many CI/CD workflows. The main Trivy project has roughly 32,000 GitHub stars, and the affected trivy-action repository has about 1,300. A compromise in that path can potentially affect many downstream organisations at once."
"The attack method is especially important. Rather than targeting victims individually, the attackers compromised the organisation behind a major supply-chain component and used its GitHub repository and mutable version tags to distribute malicious code at scale. This reflects a broader and increasingly common pattern of targeting trusted software supply-chain platforms and maintainers to reach many customers through a single upstream compromise."
"Compared with other supply chain attacks, this one stands out less for novel malware than because it marks a second compromise affecting Aqua Security's Trivy ecosystem in roughly a month, raising concern about repeated attacker access or incomplete containment. In late February and early March 2026, compromised Aqua Trivy VS Code extension releases were identified on OpenVSX. Now the trivy-action GitHub Action has been abused through moved tags to distribute malicious code in CI/CD pipelines. That makes this incident especially serious because repeated compromises of the same vendor in a short period suggest a persistent weakness, even if the overall blast radius may be smaller than in the largest ecosystem-wide attacks."
"This attack highlights a broader security problem across the industry: many organisations still allow build systems and developers to automatically pull in third-party code, dependencies and pipeline components from the internet with limited review, change control and too much implicit trust. That means a compromise of one widely used upstream project can quickly spread into many downstream environments, even when nothing appears broken."
"The broader lesson is that convenience and speed in modern software delivery have outpaced governance. Organisations need stronger controls over what external code they allow, how it is approved, how it is pinned and how changes are monitored before that code is trusted inside production or SaaS-connected environments."
"Organisations should immediately identify any repositories or workflow runs that executed the compromised aquasecurity/trivy-action, review those runs for possible secret exposure and rotate any credentials accessible to affected runners. They should also update workflows so GitHub Actions are pinned to SHAs rather than version tags, since GitHub's guidance treats SHAs as the safest immutable reference and this attack specifically abused mutable tags to deliver malicious code. More broadly, teams should reduce runner privileges and limit the secrets available to CI/CD jobs so that if a trusted action is compromised, the downstream impact on SaaS apps, cloud accounts and administrative systems is contained," Michal said.
Second breach
The warning follows a second compromise linked to the Trivy ecosystem in about a month. Security researchers reported that attackers force-pushed 75 of 76 version tags in the trivy-action repository, turning trusted references into a delivery channel for an infostealer designed to harvest secrets from GitHub Actions runners.
Reports said the payload sought SSH keys, cloud credentials, database logins, Git and Docker configuration data, Kubernetes tokens and cryptocurrency wallets. A related repository, aquasecurity/setup-trivy, was also affected, with several version tags reportedly rewritten in a similar way.
The attack appears to have relied on valid credentials rather than a flaw in Git itself. Aqua Security has said the incident stemmed from incomplete containment of an earlier breach involving malicious releases of the Trivy Visual Studio Code extension on Open VSX.
That earlier compromise was linked to a stolen Personal Access Token, which was used to take control of repository assets and publish tainted releases. Researchers said the latest campaign reused that access to manipulate tags without creating a new release or pushing to a branch, making the malicious changes less visible in normal development processes.
Wider issue
The case adds to concerns across the software industry about the use of third-party actions and dependencies in automated build systems. Many development teams allow code and components to be fetched from the internet during builds with limited review, creating a route for attackers to move from one upstream project into multiple downstream environments.
AppOmni urged organisations to identify any repositories or workflow runs that executed the compromised action, review those runs for secret exposure and rotate accessible credentials. It also recommended pinning GitHub Actions to immutable SHAs rather than version tags, and restricting the privileges and secrets available to CI/CD jobs so a breach in one trusted component does not spread further.
The compromise of mutable version tags, rather than the publication of an obviously malicious new release, underlines how attackers are increasingly exploiting trust in routine software delivery processes.