Container Security stories

Azul momentum surges as enterprise Java demand jumps
Yesterday
#
devops
#
data analytics
#
digital transformation
Azul wins a bigger enterprise foothold as FY26 bookings leap, partners expand and a Thoma Bravo-backed deal and Payara buyout widen its Java push.

Intruder adds container image scanning to cloud platform
Last week
#
virtualisation
#
devops
#
hybrid cloud
Intruder expands cloud security platform with registry-level container image scanning for AWS, Google Cloud and Azure users.

Orca Security flags AI secrets & supply chain gaps
Last week
#
malware
#
devops
#
mfa
Orca Security warns that AI credentials, vulnerable dependencies and lax pipeline controls are leaving production environments exposed across US and Europe.

ChatGPT flaw let hackers steal data via DNS queries
This month
#
firewalls
#
data protection
#
devops
ChatGPT flaw may have let attackers siphon sensitive user data via DNS queries, prompting OpenAI to issue a fix after researchers exposed the bug.

CloudCasa joins Nutanix Kubernetes platform partner catalog
This month
#
saas
#
virtualisation
#
data protection
CloudCasa adds backup, recovery and migration tools to Nutanix Kubernetes Platform Partner Catalog for hybrid and distributed workloads.

Percona & Chainguard launch supported database images
Last month
#
virtualisation
#
devops
#
digital transformation
Percona teams up with Chainguard to offer supported, hardened container images for MySQL, PostgreSQL and MongoDB databases.

HPE boosts AI security across networking & recovery
Last month
#
virtualisation
#
firewalls
#
data protection
HPE rolls out AI governance, recovery and post-quantum updates across networking and storage to strengthen cyber resilience in distributed operations.

NetRise launches Provenance to trace open source risk
Last month
#
devops
#
iot security
#
iot
NetRise unveils Provenance, a tool to trace open source maintainers and stop risky dependencies before they spread through software.

Red Hat survey finds cloud security incidents rife
Last month
#
data protection
#
digital transformation
#
cloud security
Red Hat survey finds 97% of organisations hit by cloud-native security incidents, forcing delays, higher costs and loss of customer trust.

Akamai adds AI tools to speed Zero Trust segmentation
Last month
#
virtualisation
#
firewalls
#
ransomware
Akamai injects new AI into Guardicore Segmentation to automate Zero Trust policies, curb lateral movement and shrink breach blast radius.

HPE unveils AI security tools & quantum-ready updates
Last month
#
virtualisation
#
firewalls
#
data protection
HPE rolls out new AI-aware security tools from edge firewalls to cloud recovery, aiming to tighten protection as enterprise AI spreads.

Akamai adds AI features to Guardicore segmentation
Last month
#
virtualisation
#
firewalls
#
ransomware
Akamai infuses Guardicore Segmentation with AI to automate zero trust policies and curb lateral movement across hybrid and cloud estates.

Zero Networks launches Kubernetes Access Matrix tool
Last month
#
virtualisation
#
devops
#
cloud security
Zero Networks has unveiled Kubernetes Access Matrix, a visual tool mapping cluster traffic to help teams curb lateral movement and policy sprawl.

Red Hat finds cloud security incidents hit 97% of firms
Last month
#
data protection
#
hybrid cloud
#
cloud security
Red Hat reports 97% of organisations suffered cloud-native security incidents last year, exposing basic failings in configuration and governance.
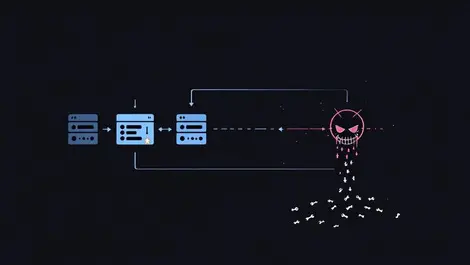
Trivy GitHub breach exposes CI/CD supply chain risk
Last month
#
devops
#
cloud security
#
application security
Aqua Security's Trivy GitHub Action was hijacked to ship infostealer code via CI/CD pipelines, exposing secrets across downstream users.

Zenarmor expands SASE platform for mobile & containers
Last month
#
virtualisation
#
firewalls
#
digital transformation
Zenarmor extends its SASE platform to mobile endpoints and containers, touting distributed, sovereign security without central cloud inspection.

Miggo & Grafana link runtime security with telemetry
Last month
#
devops
#
cloud security
#
application security
Miggo and Grafana link runtime security to Grafana Cloud telemetry, promising major cuts to critical vulnerability noise for joint users.

Keysight unveils SBOM Manager to meet new cyber rules
Last month
#
application security
#
physical security
#
devsecops
Keysight debuts SBOM Manager to automate software bills of materials as EU and US cyber rules tighten transparency and compliance demands.

Upwind brings runtime cloud security platform to Azure
Last month
#
digital transformation
#
cloud security
#
advanced persistent threat protection
Upwind integrates its runtime cloud security with Azure, offering unified protection and Sentinel tie-ins via the Microsoft Marketplace.

CrackArmour flaws in AppArmour risk Linux root access
Last month
#
cloud security
#
advanced persistent threat protection
#
physical security
CrackArmour flaws in AppArmour could let local Linux users gain root, bypass namespaces and weaken container isolation at scale.